Configuring HP iLO 2 on EL6
HP iLO Setup
HP uses a variant on IPMI called iLO, Integrated Lights-Out management. This will cover how to install and configure it for use in our cluster.
Install iLO Dependencies
The iLO tools will try to compile against all installed kernels. For this reason, remove old kernels and then ensure that the kernel sources are available.
yum list installed | grep -i kernel
dracut-kernel.noarch 004-33.2.el6_0 @updates
kernel.x86_64 2.6.32-71.el6 @CentOS/6.0
kernel.x86_64 2.6.32-71.29.1.el6 @updates
kernel-devel.x86_64 2.6.32-71.el6 @CentOS/6.0
kernel-devel.x86_64 2.6.32-71.29.1.el6 @updates
kernel-firmware.noarch 2.6.32-71.29.1.el6 @updates
kernel-headers.x86_64 2.6.32-71.29.1.el6 @updates
rpm -e kernel-2.6.32-71.el6 kernel-devel-2.6.32-71.el6
yum list installed | grep -i kernel
abrt-addon-kerneloops.x86_64 1.1.13-4.el6 @CentOS/6.0
dracut-kernel.noarch 004-33.2.el6_0 @updates
kernel.x86_64 2.6.32-71.29.1.el6 @updates
kernel-devel.x86_64 2.6.32-71.29.1.el6 @updates
kernel-firmware.noarch 2.6.32-71.29.1.el6 @updates
kernel-headers.x86_64 2.6.32-71.29.1.el6 @updates
Now we can install the kernel source and build programs.
yum install kernel-headers kernel-xen-devel kernel-devel gcc pyOpenSSL
Download and Install the HP-Provided RPMs
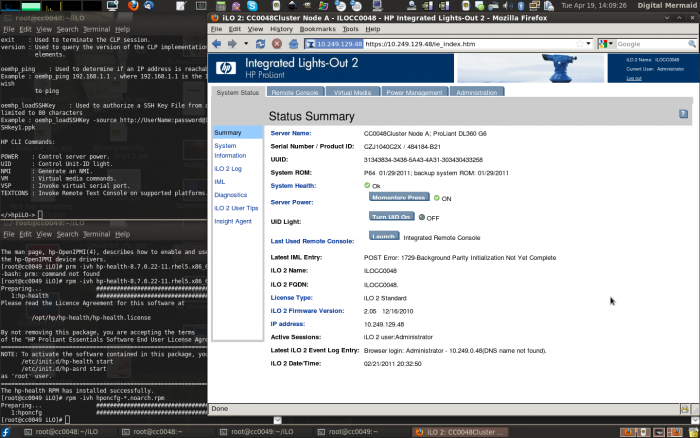
Note: This guide was written using a pair of Proliant GL360 G6 servers using iLO 2.
- Download the Proliant Support Pack.
Old
Download the following RPMs from HP directly. Note that these link outside of AN!Wiki and may go stale.
- HP iLO [ Channel Interface Device Driver]
- HP [ OpenIPMI Device Driver]
- HP [ System Health Application and Command Line Utilities]
- HP [ Lights-Out Online Configuration Utility]
Now install the RPMs:
Note: This will likely compile some drivers, generating a lot of output to the screen during the RPM install. Make sure your terminal's scroll-back buffer is sufficiently large so that you can scroll back and check for compile errors. Generally, I set my scroll-back to 5000 lines.
rpm -ivh hp-ilo-*.rhel5.x86_64.rpm hp-OpenIPMI-*.rhel5.x86_64.rpm hp-health-*.rhel5.x86_64.rpm hponcfg-*.noarch.rpm
Now check the status of the hp-ilo, hp-health and hp-asrd daemons.
/etc/init.d/hp-ilo status
Status of hp-ilo:
hpilo driver is loaded...
It's running by default.
/etc/init.d/hp-health status
Using Proliant High Performance
IPMI based System Health Monitor
hp-OpenIPMI Status:
Module Size Used by
WARNING: The hp-OpenIPMI driver does not appear to be loaded!
(hpasmxld) is stopped... [ OK ]
It is not, so start it.
/etc/init.d/hp-health start
Using Proliant High Performance
IPMI based System Health Monitor
Starting hp-OpenIPMI:
Starting Proliant High Performance
IPMI based System Health Monitor (hpasmxld): [ OK ]
Now check it again.
/etc/init.d/hp-health status
Using Proliant High Performance
IPMI based System Health Monitor
hp-OpenIPMI Status:
Module Size Used by
ipmi_si 78156 2
ipmi_devintf 44944 4
ipmi_msghandler 73560 2 ipmi_si,ipmi_devintf
(hpasmxld) is running... [ OK ]
Good, now check the HP advanced service recovery daemon.
/etc/init.d/hp-asrd status
Not Running [FAILED]
It, also, doesn't start on install so we will start it now.
/etc/init.d/hp-asrd start
Starting HP Advanced Server Recovery Daemon [ OK ]
Check that it's now running. This time we'll see it print it's PID as well as the notice that it's running.
/etc/init.d/hp-asrd status
7422
Running [ OK ]
Now make sure that they are set to start with the system.
chkconfig --list |grep -i hp
hp-asrd 0:off 1:off 2:on 3:on 4:on 5:on 6:off
hp-health 0:off 1:off 2:on 3:on 4:on 5:on 6:off
hp-ilo 0:off 1:off 2:on 3:on 4:on 5:on 6:off
Configuring The iLO BMC
Now we will configure the iLO baseboard management controller using the hp command line tools.
Basic Configuration
If all went well, you should now be able to dump the current iLO configuration to an XML file using hponcfg. What you name the file is up to you, but I like to use the system's hostname with the .xml suffix.
hponcfg -w hostname.xml
Firmware Revision = 2.05 Device type = iLO 2 Driver name = hpilo
RILOE II/iLO configuration successfully written to file "foo"
We will edit this file to set the values we want and then write the file out to the iLO BMC.
vim hostname.xml
<!-- HPONCFG VERSION = "3.0" -->
<!-- Generated 2/21/2011 14:42:32 -->
<RIBCL VERSION="2.1">
<LOGIN USER_LOGIN="Administrator" PASSWORD="secret">
<DIR_INFO MODE="write">
<MOD_DIR_CONFIG>
<DIR_AUTHENTICATION_ENABLED VALUE = "N"/>
<DIR_LOCAL_USER_ACCT VALUE = "Y"/>
<DIR_SERVER_ADDRESS VALUE = ""/>
<DIR_SERVER_PORT VALUE = "636"/>
<DIR_OBJECT_DN VALUE = ""/>
<DIR_OBJECT_PASSWORD VALUE = ""/>
<DIR_USER_CONTEXT_1 VALUE = ""/>
<DIR_USER_CONTEXT_2 VALUE = ""/>
<DIR_USER_CONTEXT_3 VALUE = ""/>
</MOD_DIR_CONFIG>
</DIR_INFO>
<RIB_INFO MODE="write">
<MOD_NETWORK_SETTINGS>
<SPEED_AUTOSELECT VALUE = "Y"/>
<NIC_SPEED VALUE = "10"/>
<FULL_DUPLEX VALUE = "N"/>
<IP_ADDRESS VALUE = "10.249.129.48"/>
<SUBNET_MASK VALUE = "255.255.0.0"/>
<GATEWAY_IP_ADDRESS VALUE = "0.0.0.0"/>
<DNS_NAME VALUE = "ILOFOOBARBAZ"/>
<PRIM_DNS_SERVER value = "0.0.0.0"/>
<DHCP_ENABLE VALUE = "N"/>
<DOMAIN_NAME VALUE = ""/>
<DHCP_GATEWAY VALUE = "Y"/>
<DHCP_DNS_SERVER VALUE = "Y"/>
<DHCP_STATIC_ROUTE VALUE = "Y"/>
<DHCP_WINS_SERVER VALUE = "Y"/>
<REG_WINS_SERVER VALUE = "Y"/>
<PRIM_WINS_SERVER value = "0.0.0.0"/>
<STATIC_ROUTE_1 DEST = "0.0.0.0" GATEWAY = "0.0.0.0"/>
<STATIC_ROUTE_2 DEST = "0.0.0.0" GATEWAY = "0.0.0.0"/>
<STATIC_ROUTE_3 DEST = "0.0.0.0" GATEWAY = "0.0.0.0"/>
</MOD_NETWORK_SETTINGS>
</RIB_INFO>
<USER_INFO MODE="write">
</USER_INFO>
</LOGIN>
</RIBCL>
Once you've edited the file to suit your network, you can write it back to the iLO BMC and the changes will then take effect. Don't bother trying to set the administrator password, it won't take. Just update the network settings. Advanced configuration will be done in the next step.
Note: This will take a minute or so to complete.
hponcfg -f hostname.xml
Firmware Revision = 2.05 Device type = iLO 2 Driver name = hpilo
<INFORM>Integrated Lights-Out will reset at the end of the script.</INFORM>
Please wait while the firmware is reset. This might take a minute
Script succeeded
Advanced Configuration of the iLO BMC
By default, you can run the initial configuration of the iLO BMC over SSH or HTTPS. We will use the web interface for this tutorial.
Note: The default iLO username is Administrator and the password will be written on a sticker on top of your server.

Open up a browser from a machine with access to the network connected to the iLO BMCs. If you ssh'ed with X-Forwarding to a server, you can start a browser like firefox.
Once connected to the browser, browse to the IP address you set either in the iLO BIOS at boot time or using the XML dump/load in the prior step.
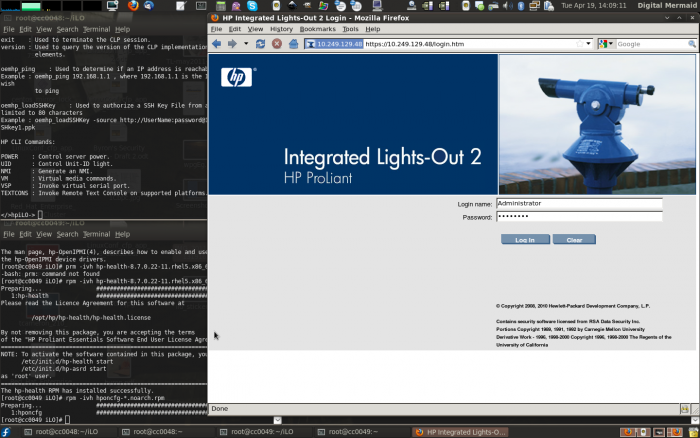
Note: The username and password are case sensitive.
One you log in, you will have access to all of the advanced configuration options.
Some Common Tasks
This will not be an exhaustive tutorial, but we will take a look at a few common values you might want to change.
Advanced Networking
To enable the iLO interface to act as a shared network interface, click on the Administration tab and browse to Settings > Network and click to select Shared Network Port. You can also configure a VLAN tag in this section.
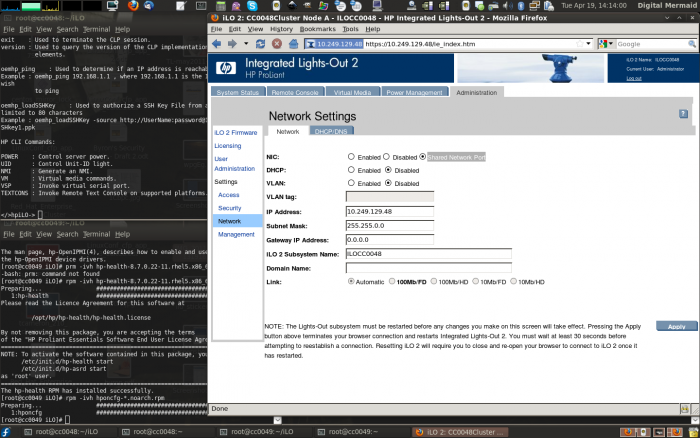
Note: Saving the changes will disconnect any open iLO sessions.
Adding the root User ssh Public Keys
Note: I've not been able to get the ssh key to be accepted.
This will allow for the root user to access the iLO BMC over ssh without needing to enter a password. This will be useful in some cases, like cluster fence device scripts.
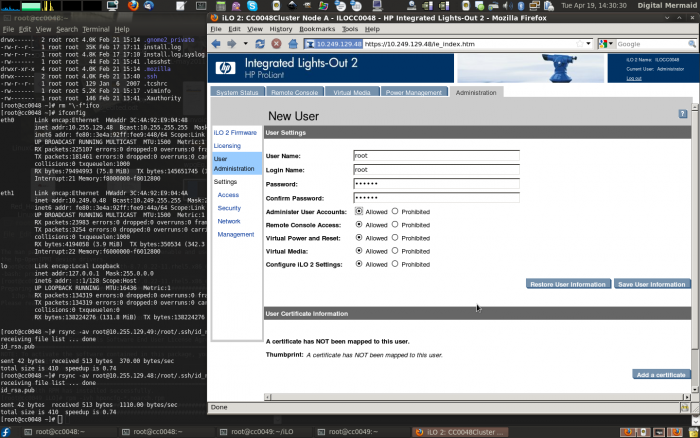
First, we need to add a user account called root to the system. I generally set this user's account to the same password as is used on the server's operating system.
Click on the Administration tab, click on User Administration and then on the Local Accounts tab.
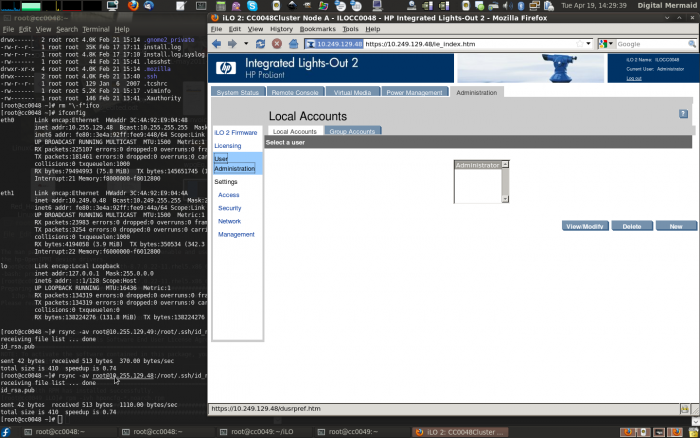
Click on the New and then fill out the form. Once done, click on the Save User Information button.
Now, copy the ~/.ssh/id_rsa.pub (or equiv.) from all hosts you want to give access to into a given directory. I generally use rsync to pull them into a file called hostname.rsa_pub_key.
Here I copy the RSA public key from two nodes.
rsync -av root@10.255.129.48:/root/.ssh/id_rsa.pub ~/cc0048.rsa_pub_key
receiving file list ... done
id_rsa.pub
sent 42 bytes received 513 bytes 1110.00 bytes/sec
total size is 410 speedup is 0.74
rsync -av root@10.255.129.49:/root/.ssh/id_rsa.pub ~/cc0049.rsa_pub_key
receiving file list ... done
id_rsa.pub
sent 42 bytes received 513 bytes 370.00 bytes/sec
total size is 410 speedup is 0.74
Now browse to the Administration tab, browse to Settings > Security and click on the SSH tab.
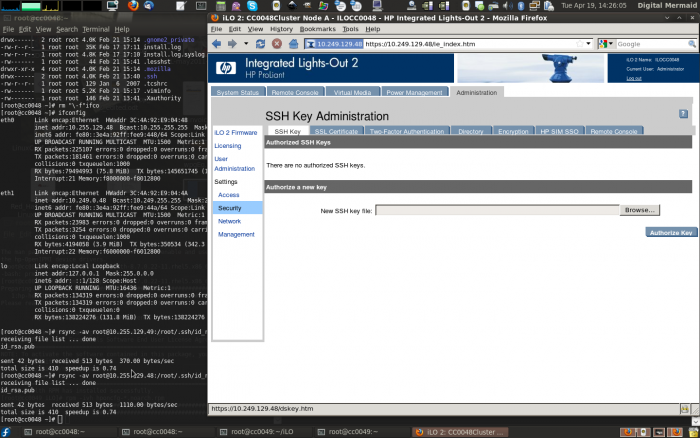
Click on the Browse button, locate and select the public key file and then click on Authorize Key.
Note: I've not been able to get the ssh key to be accepted.
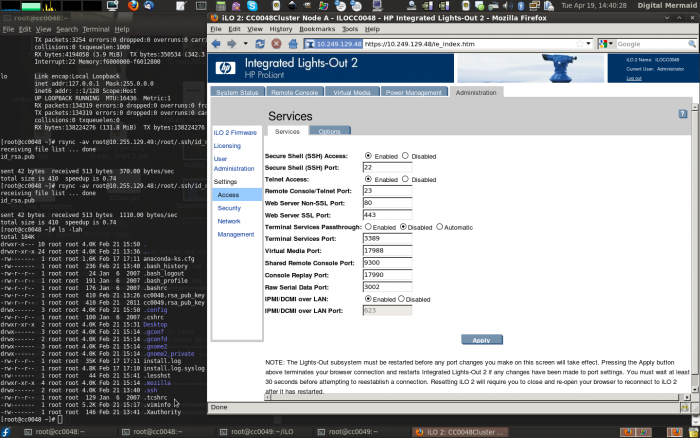
Enabling Telnet Access
To enable telnet access, click on the Administration tab, Settings > Access and click to Enable telnet.
Using fence_ilo
Warning: By default, fence_ilo uses HTTPs to connect to the iLO BMC. Under EL5, this requires that the pyOpenSSL python module be installed. If it is missing, it will fail silently. Under EL6, this is not the case.
Manually Testing fence_ilo
If everything went well, you should now be able to confirm that iLO is working by calling fence_ilo directly. In a case of a cluster, try calling status against all other nodes in the cluster.
Note: The example below resolves cc0049.ilo to the actual IP address of the iLO BMC on the target node via /etc/hosts.
fence_ilo -l Administrator -p secret -a cc0049.ilo -o status
Status: ON
Once this works from all nodes to all other nodes, you will be ready to actually use the fence_ilo fence agent.
Adding fence_ilo to /etc/cluster/cluster.conf
This is quite similar to a normal IPMI setup, if you are familiar with them. The <fencedevice ... /> tag will be similar to the example below.
<?xml version="1.0"?>
<cluster name="kp-cluster1" config_version="1">
<cman expected_votes="1" two_node="1"/>
<clusternodes>
<clusternode name="an-node01.alteeve.com" nodeid="1">
<fence>
<method name="ilo">
<device name="an1_ilo" action="reboot"/>
</method>
</fence>
</clusternode>
<clusternode name="an-node02.alteeve.com" nodeid="2">
<fence>
<method name="ilo">
<device name="an2_ilo" action="reboot"/>
</method>
</fence>
</clusternode>
</clusternodes>
<fencedevices>
<fencedevice name="an1_ilo" agent="fence_ilo" ipaddr="an-node01.ilo" login="Administrator" passwd="secret" />
<fencedevice name="an2_ilo" agent="fence_ilo" ipaddr="an-node02.ilo" login="Administrator" passwd="secret" />
</fencedevices>
<fence_daemon clean_start="0" post_fail_delay="0" post_join_delay="60"/>
</cluster>
All done! Once the cluster is up, test fencing it using the usual fence_node command.
| Any questions, feedback, advice, complaints or meanderings are welcome. | |||
| Alteeve's Niche! | Enterprise Support: Alteeve Support |
Community Support | |
| © Alteeve's Niche! Inc. 1997-2024 | Anvil! "Intelligent Availability®" Platform | ||
| legal stuff: All info is provided "As-Is". Do not use anything here unless you are willing and able to take responsibility for your own actions. | |||